
ICS Environment in Cyber Security Perspective
- ICS cyber security, ics security, ICS security perspective
In line with the revolution’s of Information Technology (IT) in the past two decades, the development of several strategic industries is also facing fast movement, the adoption of IT in the computation of infrastructure and in production operations optimization are the two main aspects that IT framework are being adopted in current era.
Since the adoption of Internet communication protocol (TCP / IP protocol) in 1982 which is considered as the backbone framework of data communication over the Internet, the growth of Internet use and digital communications era has improved exponentially. IT technology’s growth in a positive effect that being the backbone for the development of the global communication via the Internet.
Meanwhile as the development of IT technology and the use of the system was computerized in a number of industries, including the strategic industry, in this case the Oil & Gas industry, the adoption of the modern operating systems and open platform and open protocol have shift the operations philosophy on this industry. These adoption of computerized systems based on the latest IT technology is not without problems, especially when it is viewed from the security perspective of the system.
In the Oil & Gas industry, they generally use an automated control system such as Distributed Control System (DCS), Safety Instrumented System (SIS), Supervisory Control and Data Acquisition (SCADA), Programmable Logic Controller (PLC), Advanced Process Control ( APC) and Flow Computer, all of those sysmtes commonly called the Industrial Control System (ICS), as a core system that has the following main functions:
• Running the operation of a production process (oil or gas production)
• Ensure the safety aspects of the operation of the production plant
• Perform functions of monitoring and reporting, as well as data storage operations (usually it is an integrated function)
• Obtain optimal output of controlled variable with managing the operating risks into the minimum acceptable risk to ensure the safety operations of the production process
ICS consists of a variety of devices and systems which each them can operate in stand-alone mode or integrated with the other (the most common mode in the modern era), for example:
• Wind Monitoring System (Larson & Treloar system), usually a stand-alone system that functions to monitor, analyze and determine the continuity of operations of loading oil tankers
• Delta V Emerson with ABB Bailey DCS can be integrated by using the HMI as Delta V control center and operations
The ICS environment can be represented as in the attached picture,
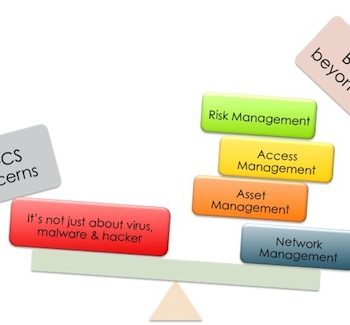
Related to the previous description where the adoption of IT infrastructure has been very diffuse in the ICS environment, the outline of the evolution of the ICS environment if viewed from cyber security standpoint are as follows,
1. Panel Based Controls
- Push buttons
- Single loop control
- Stand alone
- No networks
- No communication
2. Legacy Equipment
- Proprietary network
- Proprietary OS
- No Ethernet
- No Intranet connections
3. Modern Equipment
- Open protocols
- Ethernet everywhere
- Remote configuration
- Windows environment
- Unix/Linux platform
- Integrated system
By flash back to the period of 1970’s to the end of the 1990s, the use of ICS in such strategic industries was still very isolated and it was also totally different system compare to the development of IT technology and computerization. Generally, the ICS at that time was in form of proprietary platform, custom Operating System (OS), with a special device interfaces. Each OEM of the ICS have their own system and it was very difficult to integrate with the other systems (except with a number of intermediate systems interface which requires additional investment, including to provide with the adequate professional expertise for each system platform).
As mentioned in the previous description that the rapid development of IT technology and the computer world have brought the significant changes in the development and adoption of these platform into the ICS environment to play the significant role as the backbone of production operations in several strategic industries (in this case is the Oil & Gas industry). Hence also if ICS is viewed from the cyber security aspect, the adoption of IT and computer technology has brought a risk that could be considered a critical risk level, that giving threat to safety, financial and environment aspect of the business operations.

0 Comments